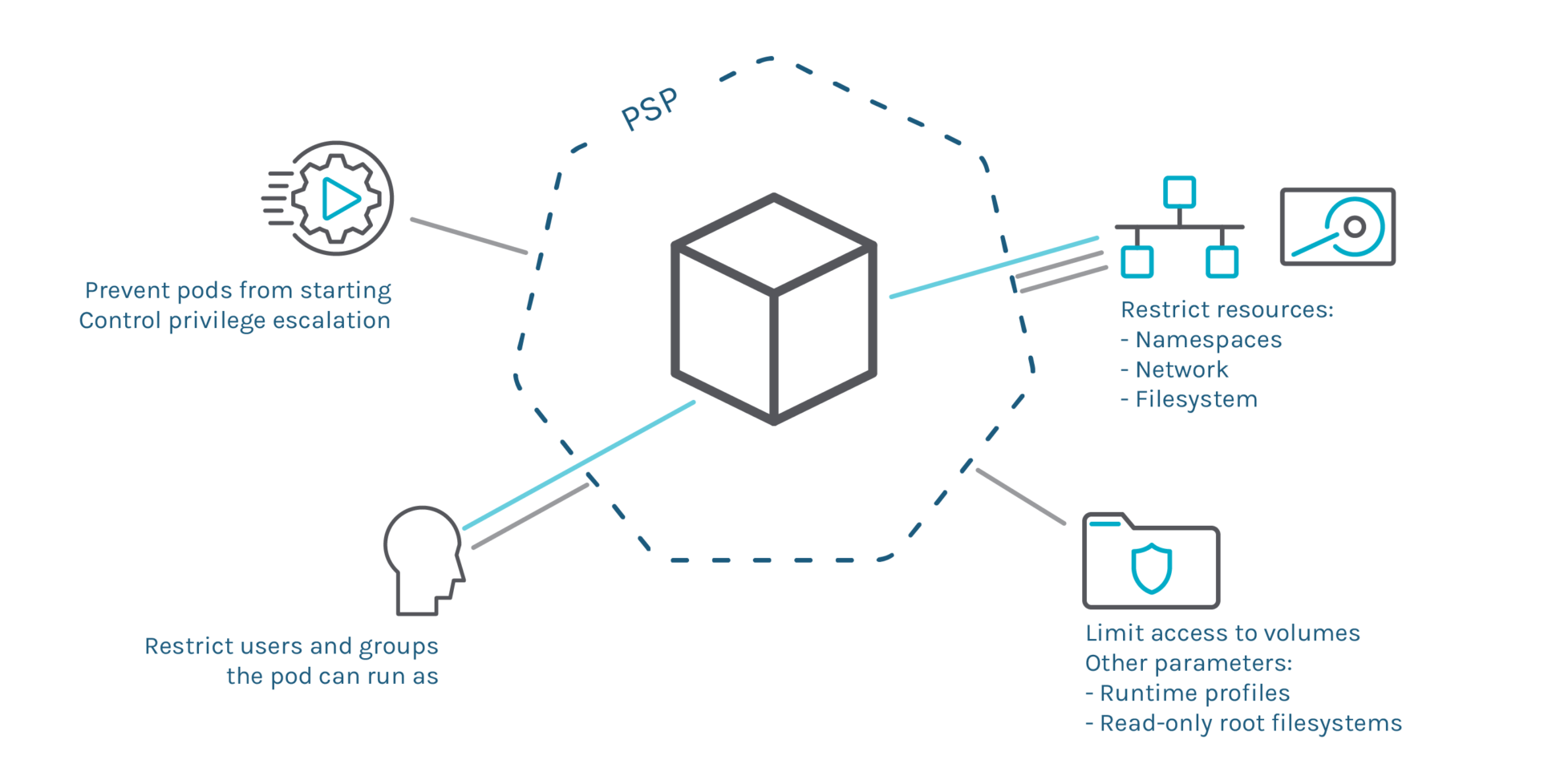
Question: PodSecurityPolicy doesn't allow Pods created by custom MutatingWebhookController that injects sidecar without securityContext.allowPrivilegeEscalation · Issue #65716 · kubernetes/kubernetes · GitHub

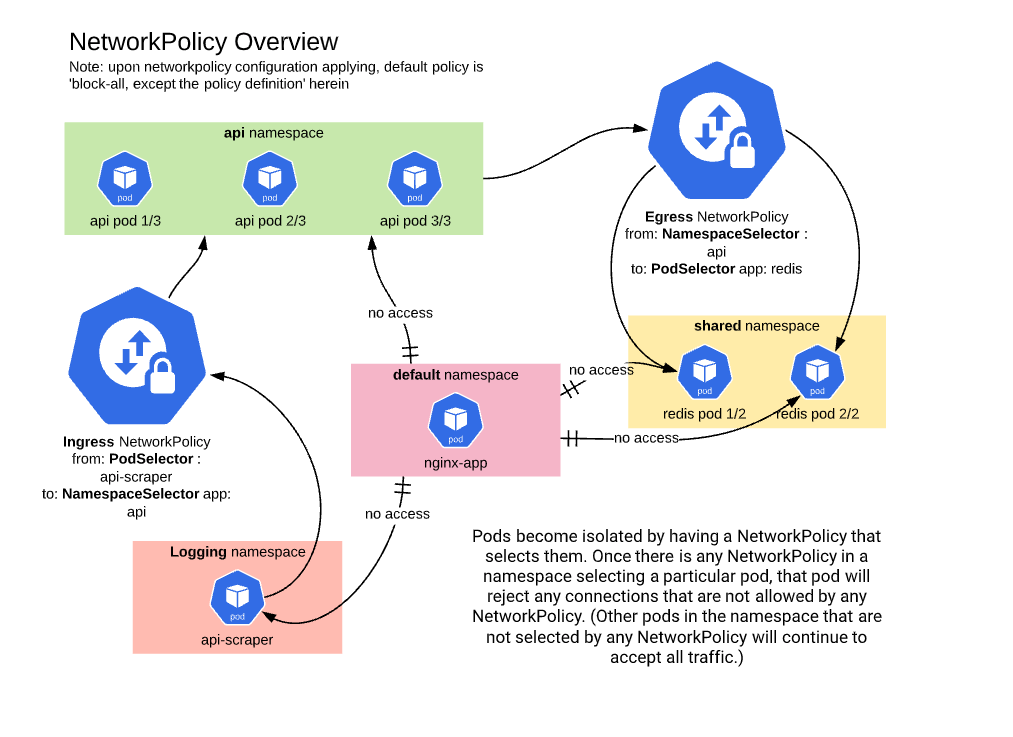
Designing a defense-in-depth network security model between Google Kubernetes Engine and Cloud SQL - DEV Community